Top 10 Anomaly Detection Software
Companies use different types of software products and systems to carry out various business activities. Although most of the available software products provide a secure platform to conduct business, companies that use software systems should consider the different factors that might threaten the security of their systems.
Users of software systems discover new vulnerabilities every day. Malicious users and applications can exploit these vulnerabilities and threaten the security of organizational data, information, and systems. Businesses need to protect their software systems from such threats by utilizing the appropriate detection systems.
Many organizations use intrusion detectors, anti-malware software and logs to secure their systems. However, software threats are unpredictable and it is difficult to secure software systems with many of the available tools. The best solution is to deploy a software system that can detect anomalies. The system can measure unusual deviations and alert users to take the necessary action.
What are the Top Anomaly Detection Software: Numenta, AVORA, Splunk Enterprise, Loom Systems, Elastic X-Pack, Anodot, CrunchMetrics are some of the Top Anomaly Detection Software.
What are the Top Free Anomaly Detection Software: Weka Data Mining, Shogun, RapidMiner Starter Edition, Dataiku DSS Community, ELKI, Scikit-learn are some of the Top Free Anomaly Detection Software.
What are Anomaly Detection Software?
Anomaly Detection Software is the identification of items, events or observations which do not conform to an expected pattern or other items in a dataset. Unsupervised anomaly detection techniques detect anomalies in an unlabeled test data set under the assumption that the majority of the instances in the data set are normal.
Supervised anomaly detection techniques require a data set that has been labeled as normal and abnormal and involves training a classifier.Semi supervised anomaly detection techniques construct a model representing normal behavior from a given normal training data set, and then testing the likelihood of a test instance to be generated by the learnt model.
Anomaly detection software allows organizations to detect anomalies by identifying unusual patterns, unexpected behaviours or uncommon network traffic. The software can compare items, events or patterns to measure deviations from the normal baseline. It can detect anomalies in a dataset that is categorized as normal.
The software can also detect anomalies in an unlabelled dataset and use a model that represents normal patterns or behaviours to locate unusual activities. The model is based on a common baseline with numerous entries of what is considered to be normal. Anomaly detection software uses different techniques including simple statistical methods, density-based techniques, and cluster-based techniques. Businesses can use the software for different purposes.
The software includes features that allow business users to identify single anomalies, collective anomalies, and contextual anomalies. It helps users to locate strange behaviours that could indicate an intrusion, monitor the health of business systems, and detect fraudulent activities in business transactions.
Some of the popular anomaly detection techniques are Density-based techniques (k-nearest neighbor,local outlier factor,Subspace and correlation-based, outlier detection, One class support vector machines, Replicator neural networks, Cluster analysis-based outlier detection, Deviations from association rules and frequent itemsets, Fuzzy logic based outlier detection and Ensemble techniques.
- Anomaly Detection: This is the most important feature of anomaly detection software because the primary purpose of the software is to detect anomalies. The software allows business users to spot any unusual patterns, behaviours or events. It can detect and monitor recurring events, trends, and correlations by deriving patents from metrics.
- Real-time Alerts: The anomaly detection feature would be a useless feature without a mechanism for alerting users when the system detects an anomaly. Anomaly software notifies users in real-time by sending alerts via emails, third-party applications and text messages. This feature allows the system administrator to react to critical alerts and train the system to stop sending alerts in case of a false positive.
- Dashboards: Anomaly detection software includes configurable dashboards that enable users to display metrics in different ways. Business users can use dashboards to visualize their data in real-time. For example, users can use a web browser to view the most important metrics in charts, lines, and bars.
- Integration: The best anomaly detection software can easily integrate with existing systems and common programming languages such as Java, PHP, Python, and C#.
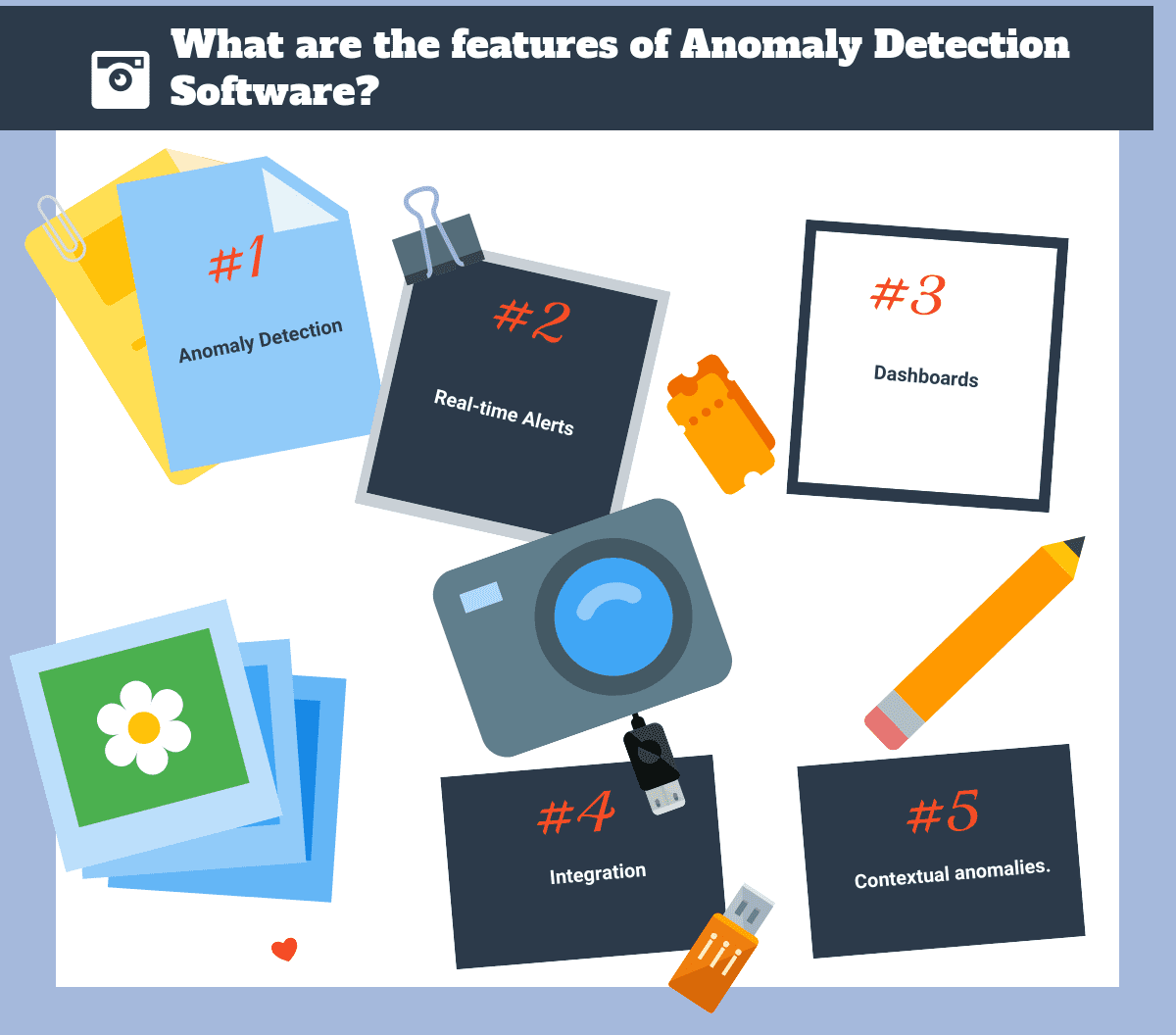
What are the features of Anomaly Detection Software?
Some of the benefits include:
- Businesses can improve the security of their software systems and important information by identifying, monitoring, and correcting anomalies.
- Users can monitor systems at the code, app or system level.
- The software can be trained depending on the needs of the user.
Top Anomaly Detection Software
Numenta
Numenta, is inspired by machine learning technology and is based on a theory of the neocortex. The technology can be applied to anomaly detection in servers and applications, human behavior, geo-spatial tracking data, and to the predication and classification of natural language. Numenta has created NuPIC (Numenta Platform for Intelligent Computing) as an open source project. Applications include detects anomalies in publicly traded companies, models stock price, stock volume, and Twitter volume related to top market companies, detects anomalies in servers and applications. Learns continuously, automatically discovers time-based patterns in data, and generalizes from experience. Early anomaly detection in streaming…
Contact for Pricing
AVORA
AVORA is a next generation data warehouse and machine learning platform, that radically changes the way business and their staff can interact through data. With AVORA your business can reduce in-house cost of analysis, reporting and hosting. And focus on commercial excellence using AVORA's real time analytics application to give you & your teams full visibility into your company performance. With over 300 connectors, there is no limit to the data we can monitor and analyse. No data modelling is required, simply plug it in and you can start analysing straight away. Easy self-service visualisation that anyone can use. Generate…
•Bring in Data From Any Source
•Write Raw SQL
•HarmonisationVisualisation
•300+ Integrations, with real-time updates and no limits.
•Visual layer to slice and dice your data
•Cloud Mobility
•Anomaly Detection and Smart Alerts
•Starting from: £400.00/month
Splunk Enterprise
Splunk Enterprise helps you gain valuable Operational Intelligence from your machine generated data. And with a full range of powerful search, visualization and pre-packaged content for use-cases, any user can quickly discover and share insights. Just point your raw data at Splunk Enterprise and start analyzing your world. Splunk User Behavior Analytics is an out-of-the-box solution that helps organizations find known, unknown, and hidden threats using data science, machine learning, behavior baseline, peer group analytics and advanced correlation. It presents results with risk ratings and supporting evidence so that an analyst and a hunter can quickly respond and take actions.…
Loom Systems
Loom Systems automatically ingests and analyzes all types of logs and metrics, learns their unique behavior over time, detects anomalies and trends, and reports these along with the root cause. The entire cycle is fully automatic, requiring no data pre-processing or manual setting of parameters and thresholds. Incidents are accompanied by recommended resolutions from a proprietary resolutions database, which also includes internal resolutions filled in by the platform users. This seamless process of knowledge retention means every recurring incident can be solved immediately. Built for low-touch operational simplicity and usability, the solution empowers IT, DevOps, System Admins, NOC teams and…
•Zero-configuration Log Parsing
•Real-time Detection of Issues
•Automated Root-cause Analysis
•Built-in Insights and Recommendations
•End-to-End Root Cause Analysis
Contact for Pricing
Elastic X-Pack
X-Pack installs as a single pack for Elasticsearch and Kibana, making it easy to do things like secure the data living in Elasticsearch or add a login screen via Kibana. X-Pack is available on Elastic Cloud, the service that lets you easily deploy the latest versions of Elasticsearch and Kibana and X-Pack features built by the creators of the Elastic Stack. X-Pack security features give the right access to the right people. IT, operations, and application teams rely on X-Pack to manage well-intentioned users and keep nefarious actors at bay, while executives and customers can rest easy knowing data stored…
•Security
•Alerting
•Monitoring
•Reporting
•Graph
•Machine Learning
Anodot
Anodot is a real time analytics and automated anomaly detection system that discovers outliers in vast amounts of time series data and turns them into valuable business insights. Using patented machine learning algorithms, Anodot isolates issues and correlates them across multiple parameters in real time, eliminating business insight latency, and supporting rapid business decisions through its uncovered insights. With its scalable SaaS platform, Anodot provides typically siloed teams BI, R&D and Devops with a single, unified system for both business and IT metrics. Automatically surfaces unusual behavior in the data. Uncovers issues both positive and negative that otherwise may have…
CrunchMetrics
CrunchMetrics is an advanced anomaly detection system, that leverages the combined power of statistical methods and AI-ML based techniques to sift through your data to identify incidents that are business critical in nature. It examines historical data to understand and establish what is ‘normal’ behavior, and then constantly monitors data streams to single out ‘abnormal’ patterns, known as anomalies. Further it analyses these anomalies in a contextual manner and correlates them with different data signals in the enterprise to understand if it is indeed a business-critical incident. Identified incidents are flagged in real-time, enabling stakeholders to act instantly, and thereby…
Automated, real-time detection
Powered by AI,ML
Self-learning algorithms
Seamless integration
Flexible output channels
Vertical agnostic solutions
Top Free Anomaly Detection Software
Weka Data Mining
Weka is a collection of machine learning algorithms for data mining tasks. The algorithms can either be applied directly to a dataset or called from your own Java code. Weka features include machine learning, data mining, preprocessing, classification, regression, clustering, association rules, attribute selection, experiments, workflow and visualization. Weka is written in Java, developed at the University of Waikato, New Zealand. All of Weka's techniques are predicated on the assumption that the data is available as a single flat file or relation, where each data point is described by a fixed number of attributes Weka provides access to SQL databases…
• Data Pre-Processing
• Data Classification
• Data Regression
• Data Clustering
• Data Association rules
• Data Visualization
Free
Shogun
Shogun is a free, open source toolbox written in C++. It offers numerous algorithms and data structures for machine learning problems. The focus of Shogun is on kernel machines such as support vector machines for regression and classification problems. Shogun also offers a full implementation of Hidden Markov models.The toolbox seamlessly allows to easily combine multiple data representations, algorithm classes, and general purpose tools. This enables both rapid prototyping of data pipelines and extensibility in terms of new algorithms. It now offers features that span the whole space of Machine Learning methods, including many classical methods in classification, regression, dimensionality…
• Free software, community-based development and machine learning education
• Supports many languages from C++, Python, Octave, R, Java, Lua, C#, Ruby, Etc.
• Runs natively under Linux/Unix, Macos, and Windows
• Provides efficient implementation of all standard ml algorithms
• Libsvm/Liblinear, Svmlight, Libocas, Libqp, Vowpalwabbit, Tapkee, Slep, Gpml and more
Free
RapidMiner Starter Edition
RapidMiner Studio provides a wealth of functionality to speed & optimize data exploration, blending & cleansing tasks – reducing the time spent importing and wrangling your data. RapidMiner provides an integrated environment for data preparation, machine learning, deep learning, text mining, and predictive analytics. It is used for business and commercial applications as well as for research, education, training, rapid prototyping, and application development and supports all steps of the machine learning process including data preparation, results visualization, model validation and optimization. Hundreds of machine learning, text analytics, predictive modeling algorithims, automation, and process control features help you build better…
•Multitude of classification and regression algorithms facilitate supervised learning
•Broad array of cluster, similarity and segmentation algorithms support unsupervised learning
•Seamless integration of R and Python scripts into workflows provide further extensibility
•Modeling capabilities and machine learning algorithms
Free
Dataiku DSS Community
Dataiku DSS is the collaborative data science software platform for teams of data scientists, data analysts, and engineers to explore, prototype, build, and deliver their own data products more efficiently. Dataiku develops the unique advanced analytics software solution that enables companies to build and deliver their own data products more efficiently. Dataiku DSS is a collaborative and team-based user interface for data scientists and beginner analysts, to a unified framework for both development and deployment of data projects, and to immediate access to all the features and tools required to design data products from scratch. The visual interface of Dataiku…
•Data connectors
•Data transformation
•Transformation engines
•Data Visualization
•Data Mining
•Machine Learning
Free
ELKI
The ELKI framework is written in Java and built around a modular architecture. Most currently included algorithms belong to clustering, outlier detection and database indexes. A key concept of ELKI is to allow the combination of arbitrary algorithms, data types, distance functions and indexes and evaluate these combinations. When developing new algorithms or index structures, the existing components can be reused and combined. ELKI is modeled around a database core, which uses a vertical data layout that stores data in column groups (similar to column families in NoSQL databases). This database core provides nearest neighbor search, range/radius search, and distance…
• Open source data mining software
• High performance and scalability
• Simple visualization window
• Data management tasks
• Standard Java API
Free
Scikit-learn
Scikit-learn is an open source machine learning library for the Python programming language.It features various classification, regression and clustering algorithms including support vector machines, random forests, gradient boosting, k-means and DBSCAN, and is designed to interoperate with the Python numerical and scientific libraries NumPy and SciPy. Classification : Identifying to which category an object belongs to Applications: Spam detection, Image recognition. Algorithms: SVM, nearest neighbors, random forest. Regression : Predicting a continuous-valued attribute associated with an object. Applications: Drug response, Stock prices. Algorithms: SVR, ridge regression. Clustering :Automatic grouping of similar objects into sets. Applications: Customer segmentation, Grouping experiment outcomes.…
Scikit-learn What are Anomaly Detection Software? Anomaly Detection Software is the identification of items, events or observations which do not conform to an expected pattern or other items in a dataset. Unsupervised anomaly detection techniques detect anomalies in an unlabeled test data set under the assumption that the majority of the instances in the data set are normal. Supervised anomaly detection techniques require a data set that has been labeled as normal and abnormal and involves training a classifier. What are the Top Free Anomaly Detection Software? Weka Data Mining, Shogun, RapidMiner Starter Edition, Dataiku DSS Community, ELKI, Scikit-learn are some of the Top Free Anomaly Detection Software. What are the Top Anomaly Detection Software? Numenta, AVORA, Splunk Enterprise, Loom Systems, Elastic X-Pack, Anodot, CrunchMetrics are some of the Top Anomaly Detection Software.


















ADDITIONAL INFORMATION
This is a great and really helpful list – thank you for sharing! I noticed that you left out Millimetric.ai though. They’re a new startup to the scene but their pricing is much more affordable than these tools.